Transforming the future of library solutions, today
With three decades of continuous innovation and together with our global community of industry leaders from academic institutions, libraries, and technology powerhouses, we are embracing generative AI, linked open data and conversational discovery.
Leverage the latest innovation to optimize library management, research, teaching and learning across the entire higher education ecosystem.
A Panorama of Solutions


By leading development in areas like conversational discovery and generative AI, stakeholders have a say in how technology like Primo and campusM Library evolve to create personalized experiences

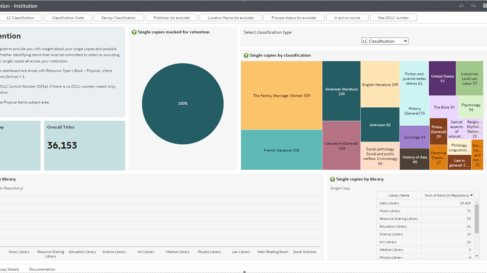
Transparency in key analytics throughout Alma’s unified solution makes it simple for institutions to access data, measure impact, make right decisions and demonstrate ROI with confidence.

When library institutions implement solutions like Rapido and campusM Library, users easily connect to all sources of information to achieve their research and learning objectives.


“It’s much easier to manage the content and troubleshoot errors, with everything in one system and CZ updates coming every week.”

Elizabeth York Rutgers University
"In the last three years, we’ve seen growth of 40% of faculty members using Leganto."
The Library Team Pontificia Universidad Católica de Chile

"...I can't imagine life or work without Alma. Too many things have changed...When we wanted to trigger the shift from print to electronic and digital, we did that with Alma."

Gijs Noels LIBIS

“With all the change we have seen … you can’t wait too long to adapt. Every five years, at least, you have to put everything on the table and rethink, from scratch.”
François Renaville University of Liège
"The unique full integration with Alma allows people to serendipitously find our content while searching the catalogue."

Alison Harvey Cardiff University
“Primo was the one place where we could integrate all the different resources that we have and give differentiated access to the different user groups.”

Knut Bøckman Royal Danish Library

"With Rapido, requests arrive in a more timely manner, and we’ve reduced our price per item."

Peggy Glatthaar Florida Gulf Coast University
“We saw a 300% usage increase, but we didn't feel that as a staff team.”

Heather Cripps University of Derby
"I don't think we would have been able to do a lot of the things that we've done without that type of customization framework."
Allen Jones The New School Library and Archives
"The adoption of Ex Libris Leganto... has led to significant improvements in workflows and streamlined access to the university library resources."

Silvia Trevenzoli University of Verona

“The immediacy of the data with campusM...means we can get early intervention going right away.“

Gary Brewerton Loughborough University
"Creating a seamless experience where we take analytics and the actions in Alma and turn them into one."

Raphael Gabbay Ex Libris, Part of Clarivate
“Whatever problems you have, don't let interlibrary loan be one of them.”

Kip Darling Birmingham City University
"Users go to Primo, find the article, and make the request right there."

Jane Campbell St Olaf College
"It has saved so much time and effort now that we have a cloud-based system."

Molly Beisler University of Nevada - Reno
"Alma lets us get materials out so much faster and so much easier"

Matthew Farthing Washtenaw Community College
"There's a lot of benefits with Rialto and I think just that transparency right there makes it worth investigating Rialto."

Jennifer Matthews Rowan University

“It has been a really big shift.. yet this was the smoothest implementation I’ve ever been through.”
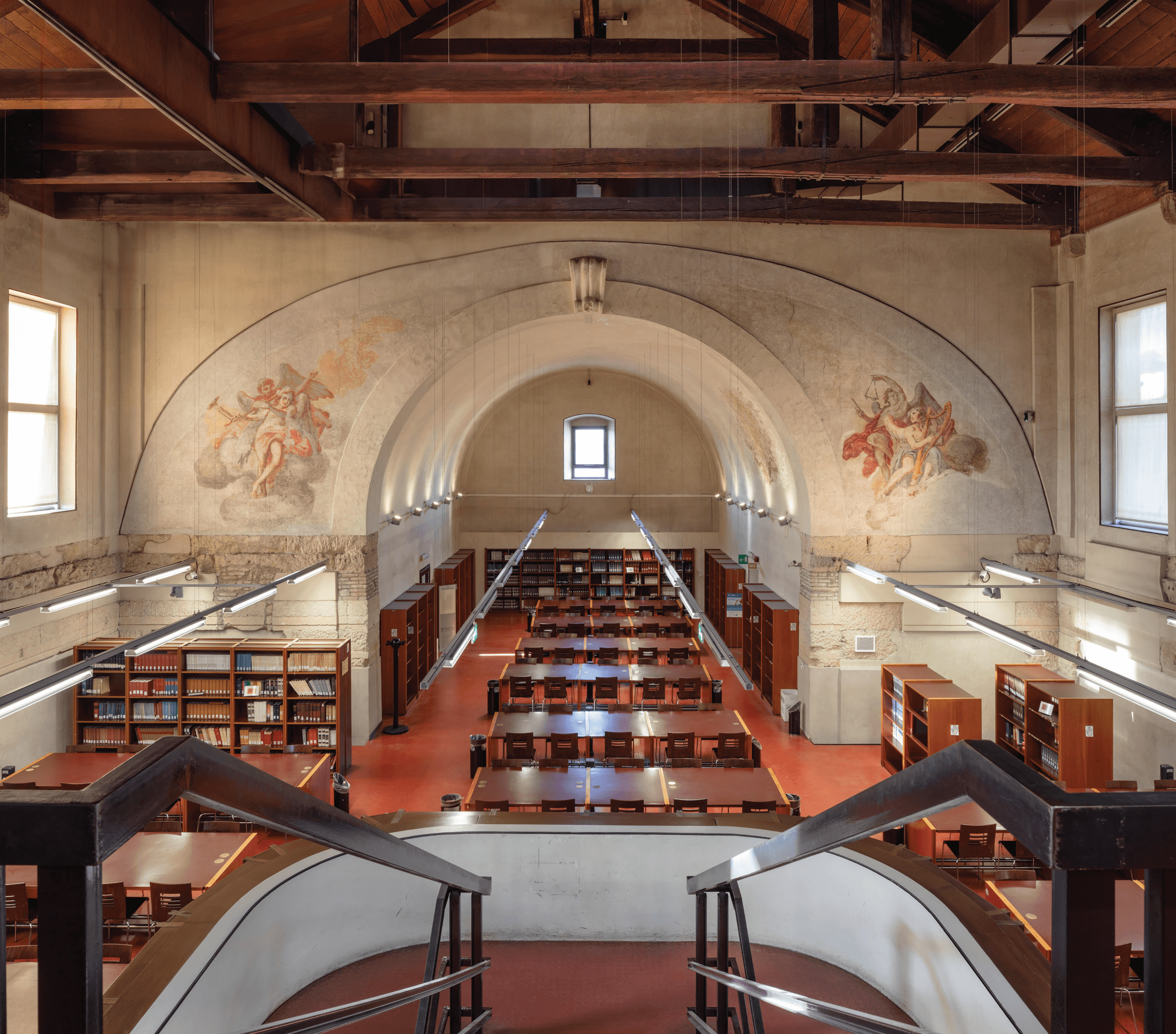
Jane Davis Linda Hall Library
"Requests [are processed] directly, without any intervention needed by ILL staff."

Rachel Watters University of Wisconsin-Madison Library
"Linked Data is a new technology and this is an important next step in the future of libraries."

Itai Veltzman Ex Libris, Part of Clarivate

“Alma and Primo have not only made our lives easier from the librarian back end, but the clients — our students — are also very happy.”

Mary Turnbull Cairnmillar Institute
"Now, students go straight to Primo, expand their results and get their materials"

Swetta Abeyta Saint Mary's College of California
"The features that excite me most about Alma are automated holdings, Alma Analytics, and the quarterly releases of new functionality."

Charlie Remy Dartmouth Library
"Our goal is to make the network open to any library using any integrated library system"

Katie Birch Ex Libris, part of Clarivate
"[Leganto] puts us in a position to be at the very forefront of course creation"

Erin Beach Northeastern University
“A small library can use Alma effectively and efficiently.”

Karen WaitE Spokane Community College
"We want to ensure that our patrons get the right materials for their studies as quickly as possible"

Christopher Lee California State University System
"My favorite thing in Alma is analytics, it's so powerful, it really helps me with assessment and figuring out how we want to change our services..."

Christina Hennessey California State University - Northridge

“…It was refreshing that the project was as quick as it was and that we were able to go live as fast as we did”
Shelly Hypes University of North Carolina

"Rapido brings resource sharing to student searches, and they don’t have to do anything else"

Matt Cox University of Derby
“Because we pay a set fee annually for RapidILL, we now have no limits on the number of articles and chapters our users can request.”

Will Grady, Collection Services Librarian Manchester Metropolitan University

“We've seen higher engagement in submissions, and can see the better user experience in those figures.”

Dr Rachel Schulkins University of Liverpool

"Among the many compliments we receive from [students], the one we hear the most is 'Thanks for supplying so quickly."

Kip Darling, Library Supervisor Birmingham City University

“We've had people saying that they’ve booked a study space on their commute, The feedback has been really positive.”
Angela Walker The University of Salford Library

“…we needed an enterprise system to support our course materials with a consistent process … Leganto had exactly what we needed.”

Director of Library Enterprise Systems Research University

"The question that we’re trying to solve with the app is: how can we make it easier for them to make the most of these opportunities?"

David Goddard, Head of Digital Experience University College London

“Our average turnaround time for articles was somewhere between 2-5 days, now they are coming in around 9 hours. That’s absolutely brilliant."

Chris Beevers University of Huddersfield


“Our continuously expanding knowledge of the new system allows us to improve our workflows, everyday IT skills, and user experience."

Sara Melchior, Art Library Manager documenta archiv

“We want to be that helping hand that gets you where you need to go.”

Dave Hyman University of San Francisco

“The campusM portal is a one stop-shop for all our students’ needs.“

Jānis Laizāns Riga Stradiņš University

“The goal was to make the digital experience as seamless as possible.”

Joseph Namey University of North Florida

“As soon as we implemented Leganto, we began using it to manage informed purchases of materials for teaching, with our integrated, cross-team workflow seamlessly handling requests.”

Angela Laurins, Library Learning Services Manager The University of Edinburgh

"Rapido brought circulation and ILL staff into a closer working relationship."

Rachel Watters, Director of Resource Sharing University of Wisconsin-Madison
"When you take a look at Alma and what Alma can do and how that can be restructured that can open your mind to new possibilities."

Julie Kane Washington & Lee University
"The University of Siena decided to go live with Alma, joining other universities in our region."

Guido Badalamenti The University of Siena
“Together with all of my colleagues in the network, and of course with the help of Ex Libris, we overcame all problems"

Wolfgang Hamedinger OBVSG
Ex Libris is privileged to be part of the DP community and is proud to share a case study of a unique institution, TIB - Leibniz Information Centre for Science and Technology.

Micky Lindlar TIB - Leibniz Information Centre for Science and Technology
"We've been able to do a lot of streamlined workflows with the same amount of staff, and we really appreciated working with the tools."

Pascal Calarco University of Windsor

"During the Covid-19 pandemic the library was one of the few services that continued to be open and to serve patrons and the whole community.”
François Renaville University of Liège
Find out how campusM is helping students at TCTC get to the right information at the right time to take the right action.

Luke VanWingerden & Dr. Mark Dougherty Tri-County Technical College

“We have the best possible relationship with Ex Libris, as we share exactly the same objective - creating valued services for our faculty.”

Ming-Jiu Hwang National Yang Ming Chiao Tung University

"Collaboration with Ex Libris has been a journey of true partnership, which we hope will continue into the future."

Thomas Marty The Swiss Library Service Platform

“After the curation is over, the output lives on.…The lists and resources are used after the fact in all kinds of ways, so the students leave a lasting legacy.”

Catherine Stephen University of Surrey

"Centralizing resource sharing through one platform gave Brandeis a better experience while lowering the administration burden."

Mark Paris Brandeis University

“This API is exactly what we were hoping for ever since we migrated to Alma.”

Brian Yost Hope College

“The campusM App Manager makes it really easy to set up this type of survey and run with it."

David Gilani Middlesex University
"Alma Analytics help highlight the value of the library's collections."

Simon Huggard Swinburne University
“The list of things we like about Alma is quite long – and getting longer, as we still have more to discover."

Bas Vat Leiden University
"The implementation of Library Mobile app allows us to be more available to our students and to provide them with all the necessary support."
Eric Lams The Library of the University of the Littoral Côte d’Opale

"What I really enjoy is the worldwide community. It makes you aware that even as a small library you are not alone.“

Christian Kieslinger University of Applied Sciences St. Pölten

“RapidILL was the perfect service at just the right time.”

François Renaville University of Liège

“We were given a very good hand from Ex Libris project management and then we managed the migration well.”

Falk Hartwig The Nuremberg University of Music

"Thanks to the Alma Community Zone, we could activate or deactivate sections of our ebook inventory at any time."

Bettina Kaldenberg Library of the University of Mannheim

“The ability to coherently manage these various constellations of licenses and patron types was one of the reasons we selected Alma."

Knut Bøckman The Royal Danish Library

"Thanks to the possibilities provided by APIs, Alma is well prepared for the future.”

Leon Krauthausen, System Librarian Freie Universität Berlin

“Ex Libris solutions helped us broaden the use of technology within the library and provide innovative learning experiences for our students.”

Dr. Brandon A. Owens Fisk University

Taking Resource Sharing to the Next Level with Rapido

Peta Hopkins, Jessie Donaghey, Sarah Fredline Bond University

"Ex Libris Alma checks off all the boxes to meet our needs and leaves us with a lot of room for growth in the future."

Judith Drescher Molloy College

“The ability for students to use both mobile apps and web browser to interact as a single platform is very powerful.”

Rabindra Das Toi Ohomai Institute of Technology

"The Alma platform has proven to be an excellent library system, smoothly integrating with other university systems."

Dalia Mendelsson Hebrew University of Jerusalem
"The major benefit is the automated processing which allows borrowing requests to be fulfilled without staff mediation."

Jacinda Boivin University of Otago

"During the first term with Leganto, almost 47,000 students were accessing reading lists in nearly 1,000 courses."

University of Sydney

"Alma has provided a different vision of the future of health libraries, allowing us to explore services beyond what we’ve previously considered."

Chris Parker The Prince Charles Hospital Library

"The Alma-based workflow is quick and efficient, from licensing all the way to getting the right content into the hands of our students."

Sarah Falls University of North Carolina School of the Arts

“Alma has made it possible for us to adapt our services and workflows so that we can operate effectively in an online environment."

Jane Saunders University of Leeds
"When you take a look at what Alma can do, and how that can be restructured, that can open your mind for new possibilities for your entire work life."

Julie Kane Washington and Lee University

"The library with the largest collection in Australia needed to streamline integration for accurate archival management."

Lynne Billington State Library of New South Wales

“Find out why an academic library at a specialist college transformed its services and operations through Alma, Primo and Leganto."

Laura Pilsel Harper Adams University

Unifying systems and workflows with Alma at the Library of Ara Institute of Canterbury

Claire Brocklehurst Ara Institutue of Canterbury

New authentication process simplifies admin and user experiences

Stephen Dashfield, Claire Hammersley University of Derby

Supporting the Imperial College Library Mission with Ex Libris Higher-Ed Cloud Solutions
Katherine Rose, Katharine Thompson, James Garry Imperial College, London

The Leganto-Rialto workflow: The key to streamlining the purchase of course materials

Angela Laurins and Elize Rowan The University of Edinburgh
Hear how Rapido meets the vision for resource sharing for some leading librarians

Mark Parris, Curran Riley, Dan Taylor Brandeis University, University of Wisconsin-Madison, Ithaca College,

Promoting Student Affordability with Leganto

Kelly Ann Sam Reserves Coordinator, California State University San Marcos
Librarians from Brandeis University and Ithaca College talk about leaving their previous resource sharing systems and moving to Rapido.

Mark Paris, Dan Taylor Brandeis University, Ithaca College
How Rapido works at a large institute with 13 campuses and part of the big ten group of libraries.

Katie Sanders Library Systems Administrator, University of Wisconsin-Madison

The Leganto Solution as a Facilitator in Cross Team Collaboration

Sarah Bateup & Moraig Vuurman Faculty Librarian, Technology Enhanced Learning Designer, Bond University
Turning resource sharing into a streamlined, user-friendly process helped benefit staff and patrons while reducing Ithaca College's costs.

Dan Taylor Library Systems Specialist, Ithaca College

"campusM allows us to stay connected and maintain an engaging and unique experience."

Francisco Esteban University of Barcelona

Alma for Digital Resources Provides Critical Digital-Based Access at the University of Liège

François Renaville, Paul Thirion, Fabienne Prosmans, Stéphanie Simon University of Liège

Alma as Part of a Strategy to Become an International-Level Institution

Celine Qiu Southern University of Science and Technology (SUSTech)

PNW seniors use campusM sandbox to improve wayfinding services

George Stefanek, Carol Coupet Purdue University Northwest

University of Mpumalanga Brings Together Two Academic Libraries with Alma

Zanele Mathe University of Mpumalanga



Students, Faculty & Staff Get the Most Out of Interlibrary Loan

Joy Pohlman University of Wisconsin-Madison
Efficiently delivering course resources and managing copyright licensing

Margaret Ann Trotter Vanderbilt University

Increasing OER use and lowering student costs

Rosemary Arneson University of Mary Washington
Alma & Summon at Johnson County Community College

Michael Frisbie Johnson County Community College

Smart & Efficient Interlibrary Loan at Harvard Library with RapidILL

Leila Smith Harvard University
Partnering with academics and educational developers

Alison Neil University of New South Wales

Demonstrating and Deepening the Library's Value with Ex Libris Higher-Ed Solutions

Helen Woolfries Kingston University London

Alma at California State University: A Consolidation of Efficiency and Savings

Jessica Hartwigsen California State University
A Faculty Perspective of Leganto – Making Course Resource Lists Easy

Sara Branch Formerly an Associate Professor of Psychology

A Fulfillment Round Table: Invisible Convenience

Brian Thompson & Todd Vandenbark University of Iowa & Wartburg College

Middlesex University Transforms Student Engagement with campusM

Mary McLaren, Student Communications Officer Middlesex University

Greater control over copyright and improved service to faculty

Susan Lafferty Australian Catholic University
Supporting teaching strategy and improving learning affordability

Pascal Calarco, University Librarian University of Windsor

Leganto at the University of Edinburgh: Improving Library Productivity and Student Experience

Angela Laurins & Sarah Ames University of Edinburgh

How can you provide a digital one-stop shop to college services for your students? Learn from Miami Dade's example.

Ewie Marais, Director of Enterprise Applications Miami Dade College

What does a successful campus app marketing plan look like? Learn how the University of Montana launched their campusM app.

University of Montana

A Resource Sharing Round Table: How Macquarie University is Streamlining Interlibrary Loan

Tony L.H. Wai
Annette Schryver
Jim Kelly
Matthew Pinson
Macquarie University

"Our students and staff really engage with campusM. They enjoy and appreciate accessing our services directly from their devices."

Iain Bruce Edinburgh Napier University

Rosetta at the National Library of New Zealand: Keeping the Nation’s Digital Heritage Secure and Accessible

Steve Knight Programme Director, Preservation Research and Consultancy, National Library of New Zealand

“Because of the streamlined back-office processes, we're able to reinvest staff time in more front-facing, student-focused activities.”

Richard Milne Robert Gordon University
Streamlining Researcher Access to Funding
Ryan Champagne Director of Systemwide Digital Library Services, California State University
An Instructor's Perspective of Leganto: Improving Teaching & Learning Effectiveness

Dr. Siobhan MacAndrew Psychology lecturer, Abertay University

“We have a vision for how the library can help the university, and Leganto has facilitated our ability to provide that help.”

Greg Argo Associate Director for Access & Digital Services, University of St. Thomas
Alma at the University of Wisconsin: The New UX and Consortium Collaboration

Crystal Buss Head of Access Services, University of Wisconsin

“Leganto makes library resources more visible and showcases the library for the entire institution.”

Asbjørn Risan BIBSYS Consortium

“Having Leganto is bringing the focus back to what the library really is, which is delivering resources and providing service.”

Jean McGuinness Library Services Team Leader, Abertay University

"Crucially, campusM helps us communicate the Aston student experience."

Tony Lyons Digital Project Manager, Aston University
"With Leganto it's a Year-Long Dialogue with the Academics"

Sinéad McGhee Academic Librarian, Abertay University
Leganto at Washington State University: Impacting Learning Affordability

Blake Galbreath Core Services Librarian, Washington State University
Primo at KU Leuven: The New Primo UI and the Primo Community

Mehmet Celik Senior Business Consultant, KU Leuven
Leganto at University of New South Wales: Creating a Community around Course Reading Lists

Cath Ellis Associate Dean of Education Faculty of Arts & Social Sciences, University of New South Wales
Rosetta at the University of Nebraska-Lincoln: Configurable Digital Asset Management

Jenny Thoegersen Data Curation Librarian, The University of Nebraska-Lincoln
Primo at City University of New York: Higher Usage of Electronic Resources and Better Indexing

Allie Verbovetskaya Web and Mobile Systems Librarian, City University of New York


























We Believe Together is Better



See our solutions in action
Visit Demo CenterOur Services
Services
Services
Services
Services